SQL injection and XSS: what white hat hackers know about trusting
Por um escritor misterioso
Last updated 17 outubro 2024

Software developers have a lot on their minds. There are are myriad of questions to ask when it comes to creating a website or application: What technologies will we use? How will the architecture be set up? What functions do we need? What will the UI look like? Especially
Software developers have a lot on their minds. There are are myriad of questions to ask when it comes to creating a website or application: What technologies will we use? How will the architecture be set up? What functions do we need? What will the UI look like? Especially in a software market where shipping new apps seems more like a race for reputation than a well-considered process, one of the most important questions often falls to the bottom of the “Urgent” column: how will our product be
Software developers have a lot on their minds. There are are myriad of questions to ask when it comes to creating a website or application: What technologies will we use? How will the architecture be set up? What functions do we need? What will the UI look like? Especially in a software market where shipping new apps seems more like a race for reputation than a well-considered process, one of the most important questions often falls to the bottom of the “Urgent” column: how will our product be

sql injection, Breaking Cybersecurity News
5 Phases of ETHICAL HACKING

Full article: Case Study: Extenuation of XSS Attacks through Various Detecting and Defending Techniques

Spidyhacker
Cross-site Scripting (XSS) Attack: All You Need to Know - Astra Security Blog
Hackers are Googling your plain text passwords: preventing sensitive data exposure

xss, Breaking Cybersecurity News

Hacking, Types, Purpose, Hackers, SQL Injection, SQLMAP

Sql injections

Apache Security: Chapter 10. Web Application Security

SQL Injection Prevention and Mitigation – The Cybersecurity Man

Network Vulnerabilities and Threats

Ethical hacking for IoT: Security issues, challenges, solutions and recommendations - ScienceDirect
Recomendado para você
-
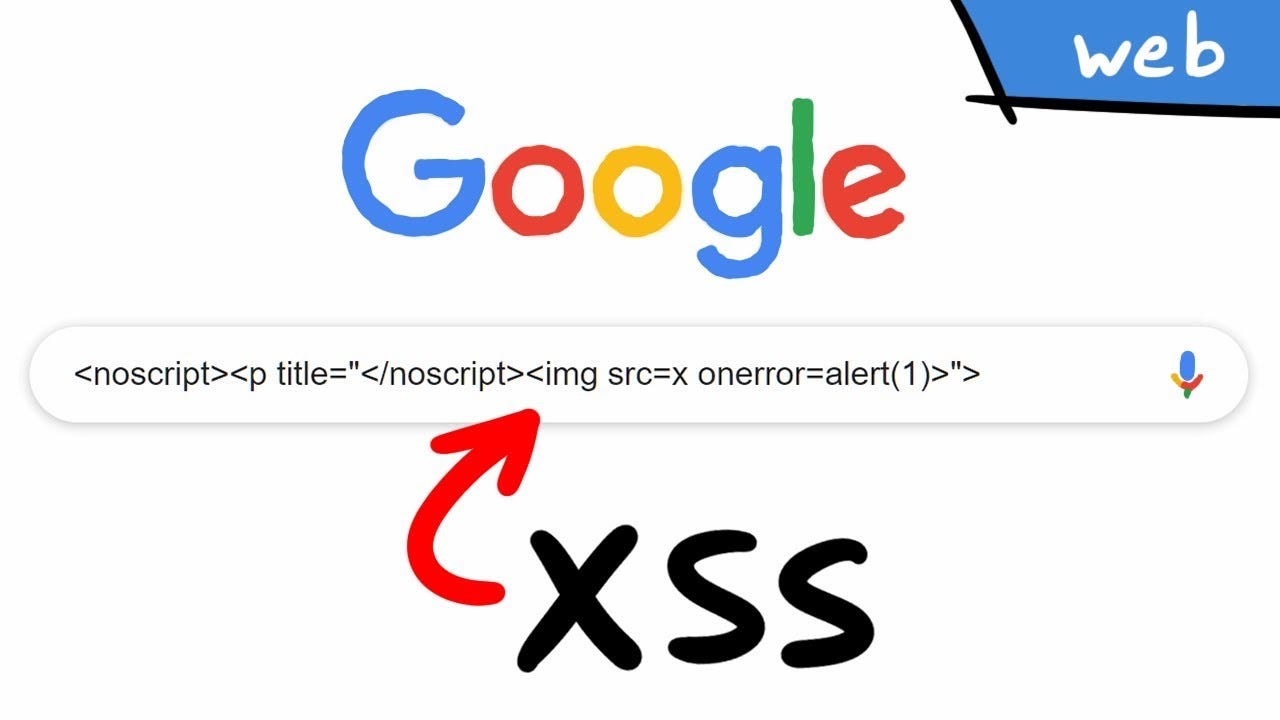 Cross Site Scripting ( XSS ) Vulnerability Payload List17 outubro 2024
Cross Site Scripting ( XSS ) Vulnerability Payload List17 outubro 2024 -
 Reflected XSS, How to Prevent a Non-Persistent Attack17 outubro 2024
Reflected XSS, How to Prevent a Non-Persistent Attack17 outubro 2024 -
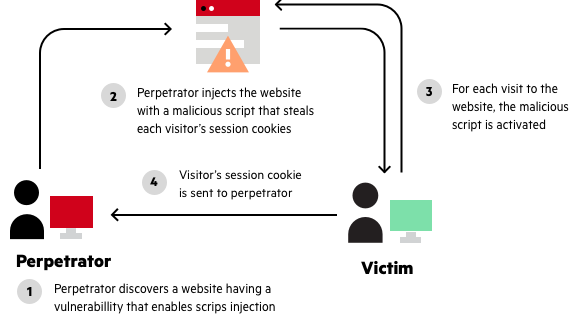
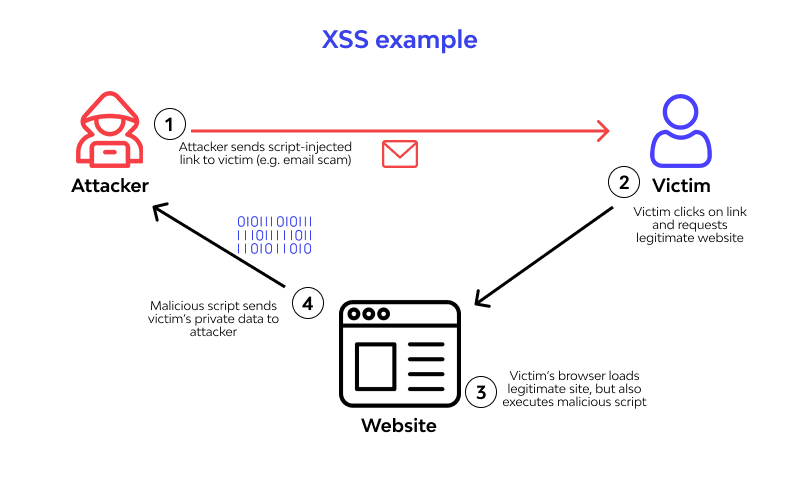 Cross site scripting (XSS) attack - Types and Examples17 outubro 2024
Cross site scripting (XSS) attack - Types and Examples17 outubro 2024 -
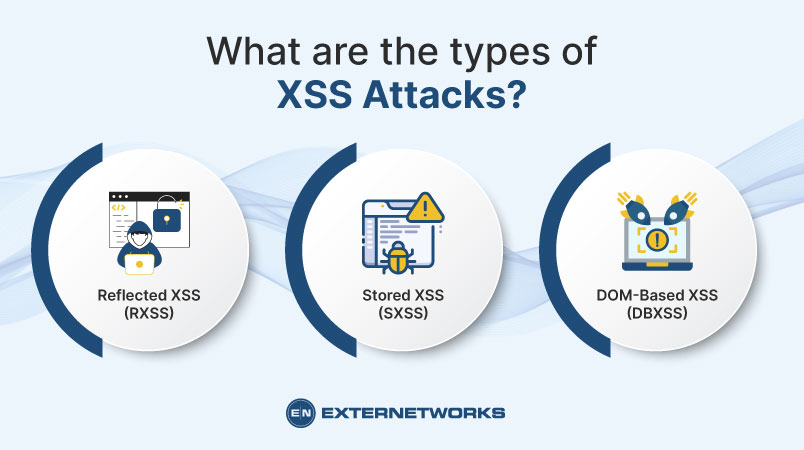 What is Cross-Site Scripting (XSS) Attacks?17 outubro 2024
What is Cross-Site Scripting (XSS) Attacks?17 outubro 2024 -
 What is Cross-Site Scripting? XSS Cheat Sheet17 outubro 2024
What is Cross-Site Scripting? XSS Cheat Sheet17 outubro 2024 -
 What Is Cross Site Scripting and How to Avoid XSS Attacks?17 outubro 2024
What Is Cross Site Scripting and How to Avoid XSS Attacks?17 outubro 2024 -
 Cross-Site Scripting: XSS Injection » Hacking Lethani17 outubro 2024
Cross-Site Scripting: XSS Injection » Hacking Lethani17 outubro 2024 -
 What is XSS or Cross-Site Scripting Attack? - The Security Buddy17 outubro 2024
What is XSS or Cross-Site Scripting Attack? - The Security Buddy17 outubro 2024 -
 XSS Attack: 3 Real Life Attacks and Code Examples17 outubro 2024
XSS Attack: 3 Real Life Attacks and Code Examples17 outubro 2024 -
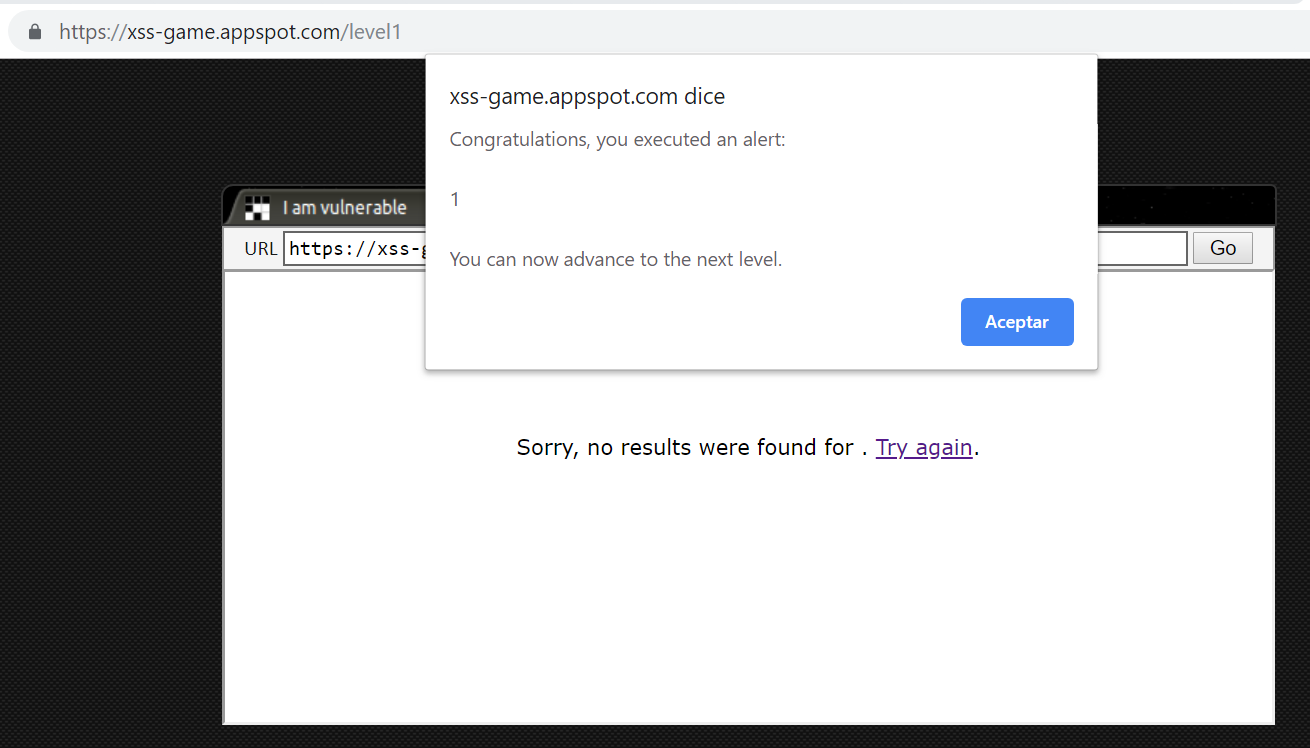
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://d3i71xaburhd42.cloudfront.net/c976c25cbfcac95b7f9ca9b5783a731a75426605/1-Figure1-1.png) PDF] Figure 1: Architecture of XSS attack Injection of code into17 outubro 2024
PDF] Figure 1: Architecture of XSS attack Injection of code into17 outubro 2024
você pode gostar
-
 Everton x Man City, 14 de maio de 202317 outubro 2024
Everton x Man City, 14 de maio de 202317 outubro 2024 -
 Activision patents reveal SBMM systems potentially used in Modern17 outubro 2024
Activision patents reveal SBMM systems potentially used in Modern17 outubro 2024 -
Will you pull off a daring escape as a Straw Hat pirate, or bring orde, ONE PIECE17 outubro 2024
-
 SCARLET WITCH - MARVEL17 outubro 2024
SCARLET WITCH - MARVEL17 outubro 2024 -
Honzuki no Gekokujou / 本好きの下剋上17 outubro 2024
-
 Evento de Halloween de Pokémon GO adicionando 2 novos tipos de fantasmas e shiny pela primeira vez17 outubro 2024
Evento de Halloween de Pokémon GO adicionando 2 novos tipos de fantasmas e shiny pela primeira vez17 outubro 2024 -
 Download wallpaper 1280x1024 laptop, screen, code, programming17 outubro 2024
Download wallpaper 1280x1024 laptop, screen, code, programming17 outubro 2024 -
/cdn.vox-cdn.com/uploads/chorus_image/image/72751352/GettyImages_1358113667.0.jpg) Medicaid enrollment dropped by nearly 9 million people in 2023 - Vox17 outubro 2024
Medicaid enrollment dropped by nearly 9 million people in 2023 - Vox17 outubro 2024 -
 Samsung Galaxy S23 Ultra17 outubro 2024
Samsung Galaxy S23 Ultra17 outubro 2024 -
 NFCYM (@NFCYM) / X17 outubro 2024
NFCYM (@NFCYM) / X17 outubro 2024

